Last updated:
 Why Trust Cryptonews
Why Trust Cryptonews

The U.S. Health Sector Cybersecurity Coordination Center (HC3) issued a critical alert on October 4 about the emergence of Trinity ransomware, a cyber threat actor that has begun targeting vital sectors, including healthcare.
According to the report, several organizations, including at least one healthcare provider in the U.S., have already been impacted.
Trinity ransomware is particularly dangerous due to its “double extortion” method, which encrypts victims’ files and steals confidential data.
Victims are pressured to pay in cryptocurrency to prevent their sensitive information from being exposed. As of early October 2024, seven organizations had fallen prey to Trinity ransomware.
Trinity Ransomware Attack: How Does It Extort Victims?
Trinity ransomware was first detected in May 2024 and is known for its advanced techniques, which exploit a variety of attack pathways.
These include phishing schemes, compromised websites, and vulnerable software.
Once it breaches a system, the malware collects important details about the infrastructure, even impersonating legitimate system operations to bypass standard security measures.
After gaining control, the ransomware scans the network, attempting to spread to other system parts.
When fully entrenched, it initiates its double extortion tactic — exfiltrating sensitive data before encrypting files.
Files encrypted by Trinity receive a “.trinitylock” extension, with a clear indicator of compromisation.
The malware employs the ChaCha20 encryption algorithm, rendering files unreadable without the necessary decryption key.
Victims are then presented with a ransom note, usually provided in text and .hta formats.
This note demands cryptocurrency payment within 24 hours, and it threatens to leak or sell the stolen data if the ransom is not paid.
Currently, no tools are known to decrypt files locked by Trinity ransomware, leaving victims with few options other than paying the ransom or seeking professional assistance for recovery.
A Rising Threat of Crypto Ransom Payments
This form of ransomware is increasingly targeting sectors like healthcare, where patient confidentiality and critical data make institutions highly vulnerable.
The report shows that seven victims have been impacted by Trinity ransomware, including two healthcare providers, one in the U.K. and another in the U.S.
The healthcare sector is particularly at risk due to the sensitive nature of patient data, making it a prime target for cybercriminals.
Knowing the urgency healthcare providers feel in safeguarding such critical information, ransomware groups like Trinity are betting that victims will choose to pay rather than risk data exposure.
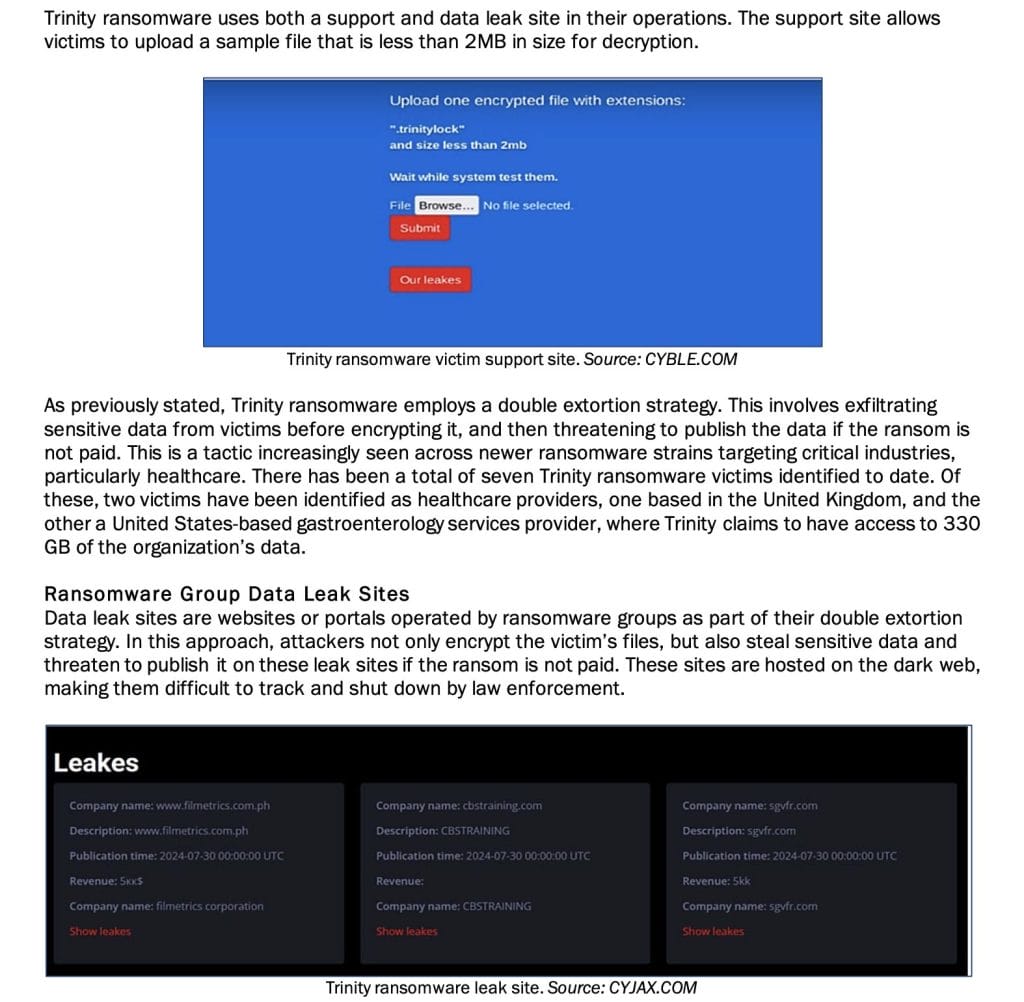
In addition to its extortion activities, Trinity operates both a support site and a data leak site.
The support site allows victims to decrypt small sample files, proving that paying the ransom will restore access to their data.
On the other hand, Trinity publishes stolen information from victims who refuse to comply on the data leak site, potentially exposing private data on the dark web.
The rise of ransomware like Trinity coincides with the increasing use of cryptocurrency in criminal activities.
According to the 2024 Crypto Crime Report by Chainalysis, ransomware payments reached $1.1 billion in 2023, as major organizations were forced to pay large sums to regain access to their data.
More than 538 new ransomware variants emerged in 2023, with notable victims including the BBC and British Airways.
Cybercriminals favor cryptocurrency for ransom payments due to its pseudonymous nature, making it challenging for authorities to track the funds.




